Top 3 Endpoint Detection and Response (EDR) Solutions and How Tech Support Austin Can Implement Them

In today’s cybersecurity landscape, Endpoint Detection and Response (EDR) solutions are crucial for protecting businesses from sophisticated threats. As your local managed service provider, Tech Support Austin is equipped to implement and manage these advanced security tools for your organization. Let’s explore the top three EDR solutions and how we can help you leverage them effectively.
Understanding Endpoint Detection and Response (EDR) and Its Importance for Your Business
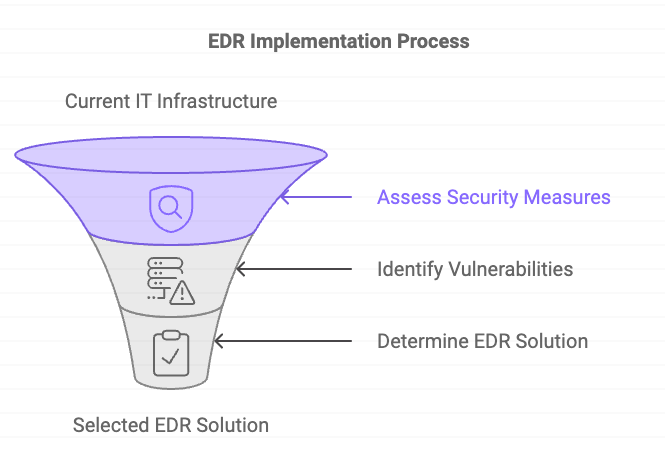
In today’s rapidly evolving digital landscape, cybersecurity threats are becoming increasingly sophisticated and prevalent. As a result, businesses of all sizes need robust security measures to protect their valuable data and systems. One crucial component of a comprehensive cybersecurity strategy is Endpoint Detection and Response (EDR).
Boost Your Starlink Internet Experience with Local Experts at Tech Support Austin

Starlink offers incredible internet access in even the most remote locations, but occasional issues like slow speeds or service interruptions can disrupt your experience. At Tech Support Austin, we specialize in optimizing Starlink setups, ensuring you get the most out of your connection. Whether you need troubleshooting, installation support, or performance enhancements, our local experts are here to keep you connected. Contact us today for a consultation and let’s get your Starlink running smoothly!
Transform Your Jira Setup with Austin’s Local Experts: Unlock Efficiency with the Right Configuration
If Jira feels more like a roadblock than a productivity tool, it’s likely due to your configuration. After helping hundreds of teams, we’ve seen these common issues:
1️⃣ Poor setup choices: Picking the wrong project type or settings leads to confusion and frustration.
2️⃣ Jira isn’t plug-and-play: It needs to be tailored to your team’s specific workflow to maximize efficiency.
3️⃣ Transform your Jira experience: When set up correctly, teams work faster and enjoy using Jira again. 🚀
Key Considerations When Selecting a Cloud Service Provider for Your Business

Learn the essential factors to consider when choosing the right cloud service provider for your business, including security, scalability, data sovereignty, and more.
Why Your Business Needs a Single Sign-On Solution: Benefits and Best Practices

Introduction: Understanding Single Sign-On Solutions In today’s fast-paced digital landscape, businesses are constantly managing a growing number of applications and systems. Each system often requires its own set of login credentials, making it cumbersome for employees to juggle multiple usernames and passwords. This not only leads to login fatigue but also heightens the risk of […]
How Attackers Exploit Hybrid Environments: Key Lessons from XM Cyber’s Latest Ebook

In today’s complex hybrid environments, attackers exploit more than just traditional vulnerabilities. They take advantage of misconfigurations, permissive identities, and security gaps that often go unnoticed. XM Cyber’s ebook uncovers these dangerous attack paths with real-world examples, providing a roadmap for organizations to protect their most sensitive assets. Step-by-Step Breakdown of Real Attacks: Each of […]
Remote Work for Your Law Firm in 2025?

Effective Remote Work for Your Law Firm in 2025: Everything You Need to Know! The legal industry underwent a significant transformation during the COVID-19 pandemic, with one of the most notable changes being the shift towards virtual and remote work. This shift has not only reshaped how legal services are delivered, but has also highlighted […]
The Hidden Costs of Technology as a Solopreneur: What You Need to Know

The Hidden Costs of Technology as a Solopreneur: What You Need to Know Running a business on your own as a solopreneur has its undeniable perks—freedom, flexibility, and the ability to set your own rules. However, with these benefits come hidden costs, particularly when it comes to technology. These expenses can catch you off guard […]
Action Required: Enable Multifactor Authentication

In today’s rapidly evolving digital landscape, safeguarding your business against cyber threats is more critical than ever. One of the most effective ways to protect your accounts and sensitive data is by enabling multifactor authentication (MFA). At Tech Support Austin, we’re committed to helping our clients stay ahead of these challenges by ensuring their IT environments are secure and resilient.
Starting in 2024, Microsoft will enforce mandatory MFA for all Azure sign-ins and other administration portals. This requirement will roll out in phases, impacting various applications and tools that your business might be using. Here’s what you need to know and how to prepare.



