In today’s rapidly evolving digital landscape, cybersecurity threats are becoming increasingly sophisticated and prevalent. As a result, businesses of all sizes need robust security measures to protect their valuable data and systems. One crucial component of a comprehensive cybersecurity strategy is Endpoint Detection and Response (EDR). This blog post will explore what EDR is, why it’s essential, and how Tech Support Austin can help implement this vital technology for your organization.
What is Endpoint Detection and Response (EDR)?
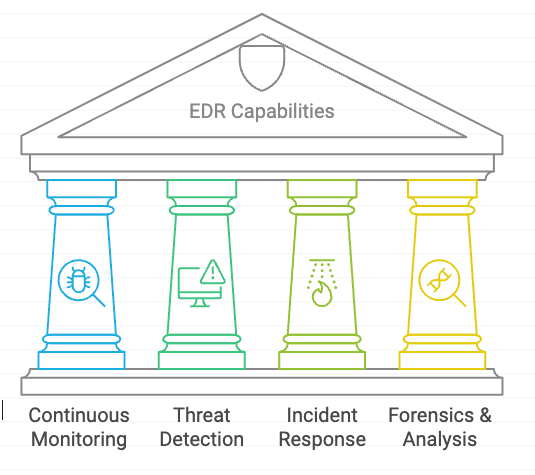
Endpoint Detection and Response (EDR) is a cybersecurity technology that continuously monitors and responds to threats on endpoints such as computers, laptops, mobile devices, and servers1. EDR solutions provide real-time visibility into endpoint activities, enabling organizations to quickly detect, investigate, and respond to potential security incidents2.Key features of EDR include:
- Continuous monitoring of endpoint activities
- Advanced threat detection using machine learning and behavioral analysis
- Automated incident response capabilities
- Forensic analysis tools for investigating security incidents

Why is EDR Important for Your Business?
Implementing an EDR solution offers several critical benefits for your organization:
- Enhanced Threat Detection: EDR systems use advanced algorithms to detect both known and unknown threats, providing a more comprehensive security approach than traditional antivirus software3.
- Rapid Incident Response: With real-time monitoring and automated response capabilities, EDR solutions can quickly contain and mitigate potential security breaches, minimizing damage to your systems2.
- Improved Visibility: EDR provides detailed insights into endpoint activities, allowing your IT team to better understand your organization’s security posture and identify potential vulnerabilities1.
- Compliance Support: Many industries have strict data protection regulations. EDR can help your organization meet these requirements by providing detailed audit trails and incident response capabilities3.
How Tech Support Austin Can Implement EDR for Your Team
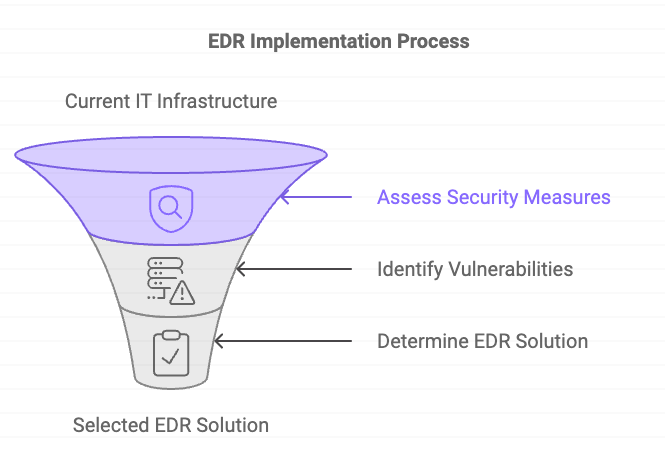
As your local managed service provider, Tech Support Austin specializes in implementing cutting-edge cybersecurity solutions tailored to your organization’s needs. Here’s how we can help you deploy an effective EDR system:
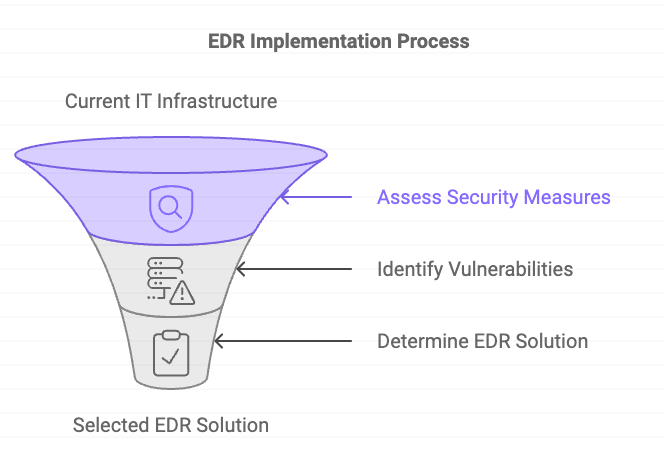
- Assessment and Planning: We’ll start by evaluating your current IT infrastructure and security needs to determine the most suitable EDR solution for your business2.
- Solution Selection: Based on our assessment, we’ll recommend an EDR platform that aligns with your organization’s size, industry, and specific security requirements3.
- Deployment and Configuration: Our team will handle the installation and configuration of the EDR solution across all your endpoints, ensuring seamless integration with your existing security tools2.
- Ongoing Monitoring and Management: We provide continuous monitoring of your endpoints, analyzing alerts and responding to potential threats in real-time1.
- Training and Support: We’ll train your team on how to effectively use the EDR solution and provide ongoing support to address any questions or concerns3.
- Regular Updates and Maintenance: To keep your EDR system effective against evolving threats, we’ll perform regular updates, apply patches, and refine detection algorithms2.
Conclusion
In an era where cyber threats are constantly evolving, implementing a robust EDR solution is crucial for protecting your business’s valuable assets and data. By partnering with Tech Support Austin, you can ensure that your endpoints are continuously monitored and protected against potential threats, allowing you to focus on your core business activities with peace of mind.Don’t leave your cybersecurity to chance. Contact Tech Support Austin today to learn more about how we can help implement an effective EDR solution for your organization.